Artificial intelligence has been “about to transform cybersecurity” for several years running. In 2026, that transformation is actually happening, but not in the way most of the hype suggested.
AI hasn’t replaced penetration testers. It hasn’t made security testing a solved problem. What it has done is quietly and substantially change how skilled security professionals work: what they spend time on, how much ground they can cover, and how quickly findings turn into finished reports. If you’re a pentester or a security manager trying to understand what’s real versus what’s marketing, this is the honest version.
The Numbers Are Real
Let’s start with some concrete data points.
A 2025 Gartner forecast projected that by 2027, more than 40% of penetration testing activities at large enterprises will incorporate AI-assisted automation in some form. A report from Bishop Fox found that AI tooling reduced average time-to-report on mid-scope engagements by 35%, with most of the savings coming from reconnaissance and report drafting. A 2026 HackerOne survey of their bug bounty community found that researchers using AI-assisted tools submitted 28% more valid reports per month than non-users, with severity distributions skewing higher.
These aren’t theoretical numbers from lab benchmarks, but instad they reflect what practitioners are actually experiencing in real engagements. The efficiency gains are real and measurable.
But there’s a catch in that same HackerOne survey: 54% of respondents said they lacked the skills to effectively prompt, evaluate, and course-correct AI tools during offensive security work. Productivity gains are only available to the people who know how to use these tools well.
What AI Is Actually Good At in Pentesting
It helps to think about where AI has genuinely moved the needle, rather than treating it as a monolithic capability.
Reconnaissance and attack surface mapping. This is where AI has arguably had the biggest impact. A mid-sized SaaS company today might expose 300+ endpoints, a microservices architecture with 40+ internal APIs, and cloud assets across multiple providers. Covering that surface manually was already becoming impossible. AI-powered recon pipelines (using tools like Subfinder, Amass, and Nuclei augmented with LLM reasoning) can map attack surfaces dramatically faster than human-only workflows.
Command generation and tool orchestration. Experienced pentesters know which tool to reach for and roughly what flags to use. But remembering the exact syntax for every nmap script, every sqlmap option, every Burp extension configuration is genuinely tedious. AI assistants that can translate “check this endpoint for auth bypass” into well-formed commands remove friction from the testing loop without removing the human judgment behind the goal.
Vulnerability documentation. Once a finding is confirmed, writing it up clearly (severity, CWE classification, reproduction steps, business impact) is important but time-consuming work. AI is quite good at drafting structured finding descriptions, especially when it has the command output and context to work from. This is one of the most underappreciated time-savers in modern pentesting workflows.
Report drafting. The Bishop Fox data showing 35% time-to-report reduction isn’t surprising when you consider how much of report writing is templated work: executive summaries, methodology sections, remediation recommendations. AI handles the boilerplate well, freeing pentesters to focus on the analysis that actually requires their expertise.
The Agentic Shift: From Copilots to Autonomous Testing
The terminology that matters most right now is the distinction between a copilot and an agent. A copilot advises: it suggests the next step, and a human decides whether to run it. An agent takes action: it runs commands, reads output, decides what to do next, and loops back around.
The field has shifted decisively toward agents in 2026, and some of the benchmark results are striking. XBOW’s autonomous agent reached the top of HackerOne’s leaderboard with over 1,000 valid submissions. In a controlled test, a system called ARTEMIS outperformed nine out of ten human pentesters on a live enterprise network — at a cost of roughly $18 per hour of operation.
These results are real, but they come with important caveats. Controlled benchmark environments have cleaner success criteria than production targets. Real engagements involve unpredictable configurations, weird network conditions, stateful application logic, and sometimes active defenders. The gap between “excels on a benchmark” and “handles your client’s multitenant SaaS app reliably” is still significant.
The best autonomous tools understand this. Responsible platforms now build in explicit trust and safety controls, letting operators define the scope, lock down destructive commands, and maintain an evidence chain. The more autonomous the workflow, the more important it becomes that a human can define the goal, inspect the evidence, and stop the agent before it does something unintended.
What AI Still Can’t Do
This is where most coverage gets it wrong by omission. The hype tends to focus on what AI can do; the honest guide also covers where it falls short.
Business logic. This is the clearest limitation. No AI system currently on the market can reliably understand that User A shouldn’t be able to access User B’s invoices, or that a low-severity file upload combined with a misconfigured S3 bucket creates a critical data breach path. Business logic is inherently contextual and it requires understanding what a system is supposed to do, not just how it behaves technically. This is still firmly in human territory.
Novel exploit chains. AI is good at recognizing known vulnerability patterns. It’s much weaker at the creative, hypothesis-driven thinking that discovers genuinely novel attack paths — the kind of work that experienced red teamers do when they go off-script and follow their instincts.
Adversarial environments. Benchmarks don’t simulate active defenders who adapt in real time. Deception, lateral thinking, and operational security under pressure remain human strengths.
Contextual judgment. Understanding what a vulnerability actually means to a specific business, its operational impact, its regulatory implications, its realistic exploitability given environmental controls - requires contextual reasoning that current AI tools don’t reliably provide.
As one of the sharper summaries from recent industry writing put it: “The strongest products have stopped pretending that AI alone is the answer.” The best 2026 programs are layered, not monolithic. AI handles breadth and volume, humans provide depth and judgment.
How This Changes What Clients Should Expect
If you’re a security manager commissioning penetration tests, this landscape has practical implications.
First, AI-augmented testing isn’t a downgrade. A skilled pentester with AI tooling covers more surface area, moves faster through routine reconnaissance, and delivers findings documentation more consistently than the same pentester working manually. The creative, judgment-intensive work gets more attention, not less.
Second, the reporting piece is genuinely better. AI-assisted findings documentation and report generation means clients should expect more consistent formatting, clearer reproduction steps, and faster turnaround. All without losing the analytical quality that comes from human review.
Third, annual point-in-time testing is increasingly insufficient on its own. AI tools have enabled continuous and more frequent testing models that weren’t practical before. Organizations that still test only once a year (and industry data suggests that’s roughly 32% of companies) are operating with a security posture that doesn’t reflect how quickly their attack surface changes.
Where PentestPad Fits In
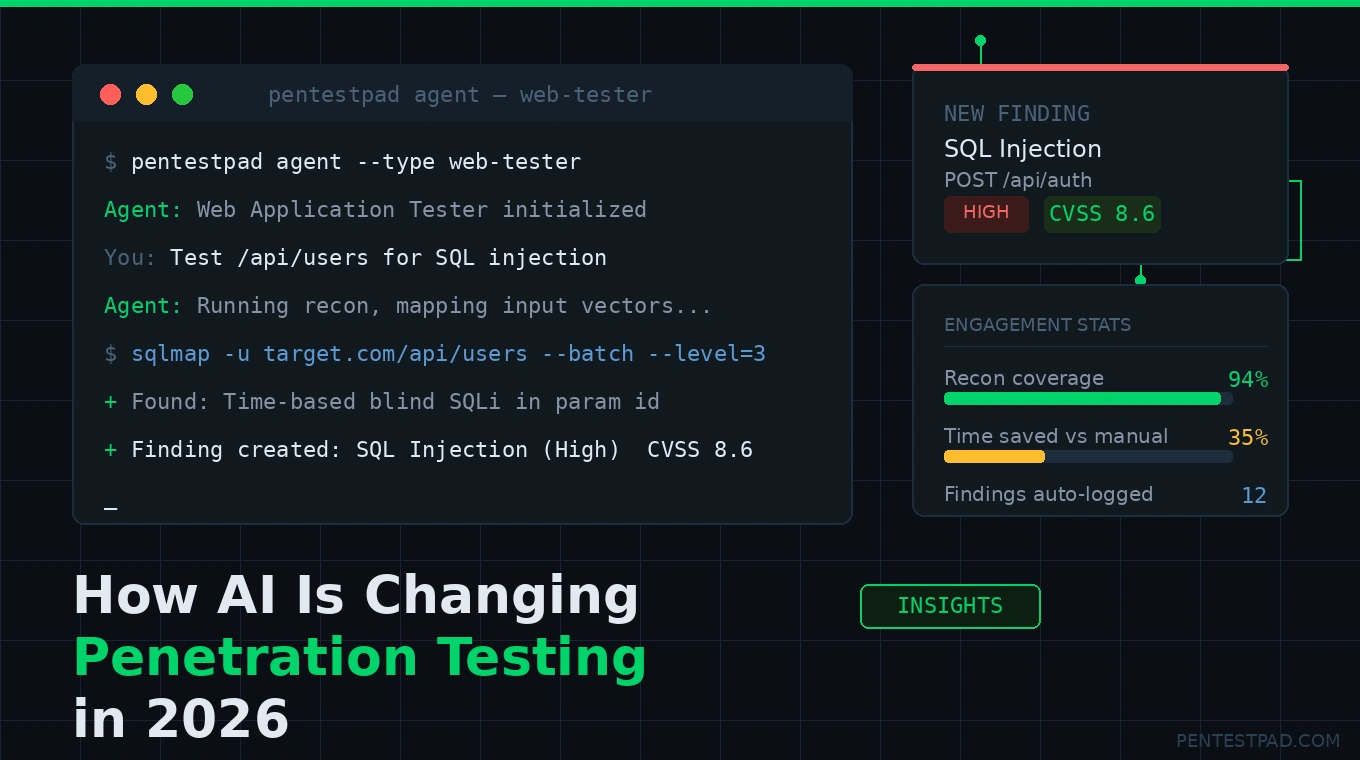
We’ve been building with this reality in mind. PentestPad Agent is a CLI-based AI assistant purpose-built for real penetration testing workflows. It’s not a generic AI chat, but a tool that understands offensive security methodology and integrates directly with the tools your team already uses.
The agent covers six specialized domains: web application testing, network pentesting, API security, mobile app testing, recon, and general assistance. It suggests and runs the right tools with the right flags, and when a finding is confirmed, it creates a structured entry in your PentestPad project automatically (with severity, CWE classification, and reproduction steps already populated).
The trust level system addresses the autonomy question directly: from requiring explicit approval for every command, up to full automation mode for CI/CD pipelines. You decide how much the agent can do on its own, and destructive commands are always blocked regardless of trust level.
The workflow closes the loop that manual testing leaves open: from the first terminal command to a finished, branded report. With the AI handling the documentation overhead and the pentester handling the judgment calls.
You can request early access at pentestpad.com/agent
The Verdict
AI in pentesting in 2026 is very useful, yet not transformative in the “replace the expert” sense, but meaningfully impactful in the “make the expert faster and more thorough” sense. The productivity gains are real. The coverage improvements are real. The report generation time savings are real.
The practitioners who are pulling ahead are the ones who’ve learned to use AI as a force multiplier on top of deep technical fundamentals. Allowing them to cover more surface area, spending less time on documentation, and focusing their human attention where it actually matters.
Want to see AI-assisted pentesting in practice? Schedule a demo of PentestPad or explore the PentestPad Agent documentation.


